What is a Credit Card Enumeration Attack? What Every E-Commerce Business Owner Needs to Know

As online sales continue to grow, so do the threats targeting e-commerce platforms. Among these threats is a lesser-known but highly damaging tactic: the credit card enumeration attack. If you’re running an online store, it’s critical to understand what this attack is, how it works, and what you can do to prevent it.
Let’s break it down in plain language—without the jargon—and get straight to what matters for your business.
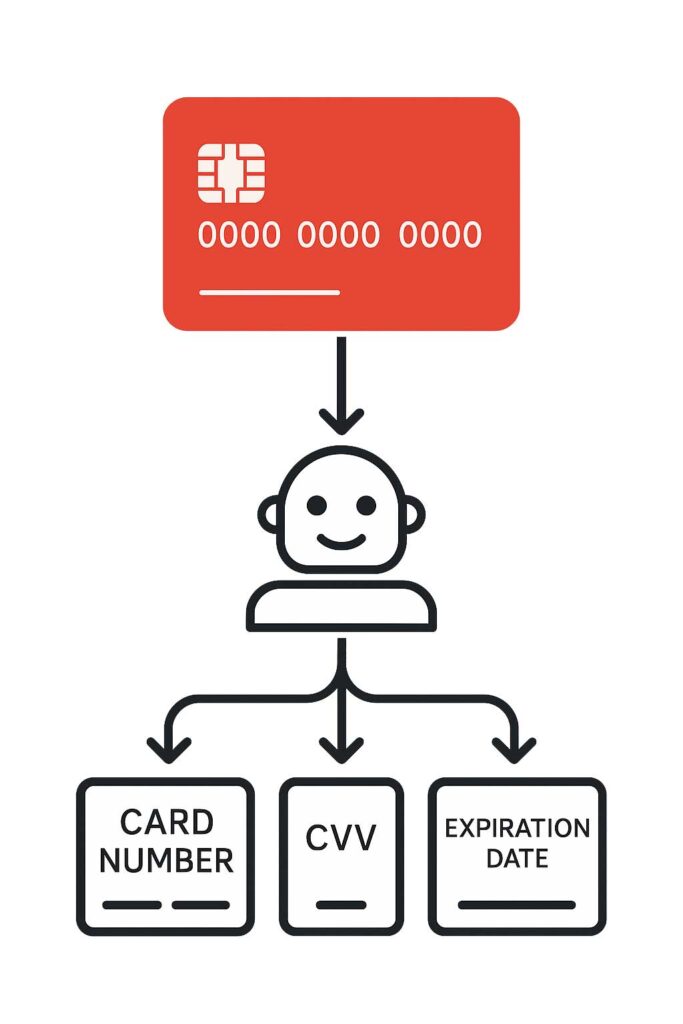
What is a Credit Card Enumeration Attack?
A credit card enumeration attack is a method used by cybercriminals to guess valid credit card details through repeated trial and error. These attackers typically automate the process, using bots to test thousands of combinations of credit card numbers, expiration dates, and CVV codes on websites with payment forms.
The goal? To piece together a working card profile that can later be used for fraudulent purchases, often on your site or others like it.
How These Attacks Work
Here’s how a typical enumeration attack plays out:
- Step 1: Card Number Validation
Attackers start by generating a large set of potential credit card numbers. They use the Luhn algorithm—a simple checksum formula used to validate a variety of identification numbers—to eliminate obviously invalid numbers. - Step 2: Testing Expiration Dates and CVV Codes
They then try different combinations of expiration dates and CVV numbers through your checkout form or payment API, looking for responses that confirm validity. - Step 3: Verifying Additional Fields
Some attackers even go further by confirming billing ZIP codes or bypassing 3D Secure (3DS) if it’s not enforced.
To avoid detection, attackers will often distribute their requests across multiple websites or use proxy networks to simulate real users.
Why E-Commerce Sites Are a Prime Target
E-commerce sites, especially those using real-time payment gateways, offer attackers a fast feedback loop: submit a card combo and get an immediate “approved” or “declined” response.
Many smaller and mid-sized online retailers lack robust fraud detection systems, making them easier targets. Even large platforms can be vulnerable if their checkout forms don’t enforce strict validation and rate-limiting controls.
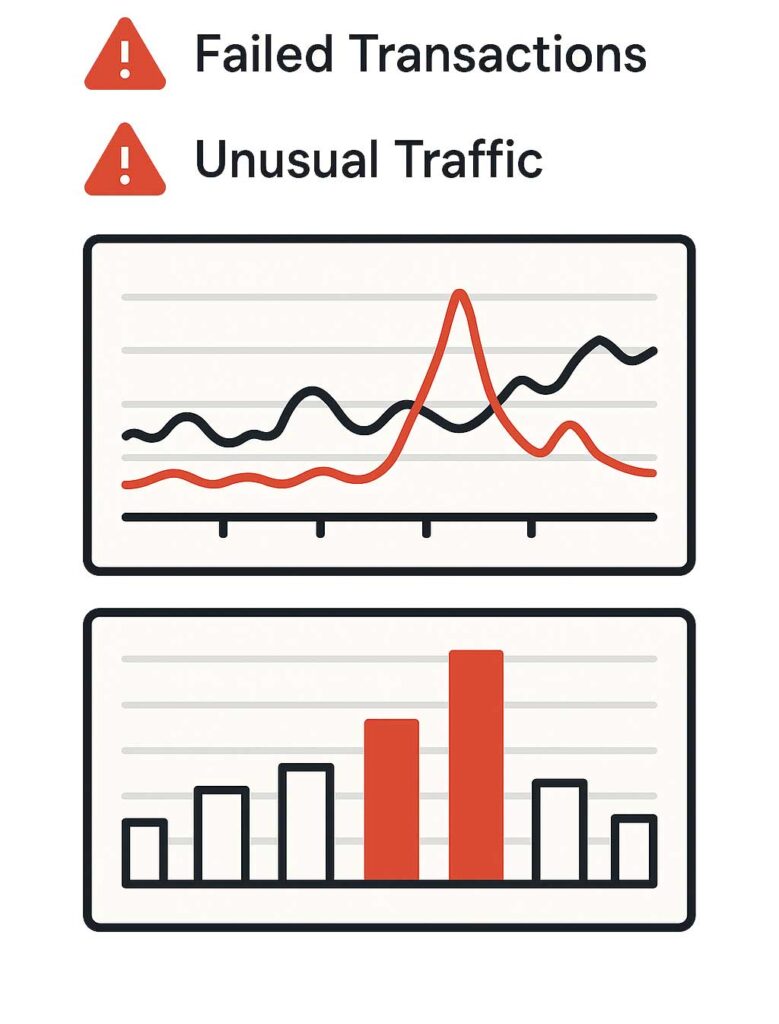
Signs Your Website Might Be Under Attack
Not sure if this is happening to your store? Watch for these warning signs:
- A sudden spike in failed payment attempts or declined transactions
- An influx of low-value purchases or test charges
- Increased chargebacks from payment processors
- Suspicious traffic patterns, especially involving bots or unusual IP locations
These signs are easy to overlook—but they can quickly snowball into serious financial and reputational damage.
Business Risks and Consequences
Enumeration attacks can cause real harm to your business. Here’s how:
- Chargebacks and Fees: When fraud happens, you’re on the hook for the loss, not the attacker. Repeated chargebacks can lead to fines or higher processing fees.
- Processor Penalties: Get flagged for too much fraud, and your payment processor might suspend or terminate your account.
- Brand Damage: Even if customer data isn’t stolen directly, news of fraud on your site erodes trust.
- Legal Liability: If it’s found that your business didn’t take reasonable steps to prevent fraud, legal consequences may follow.
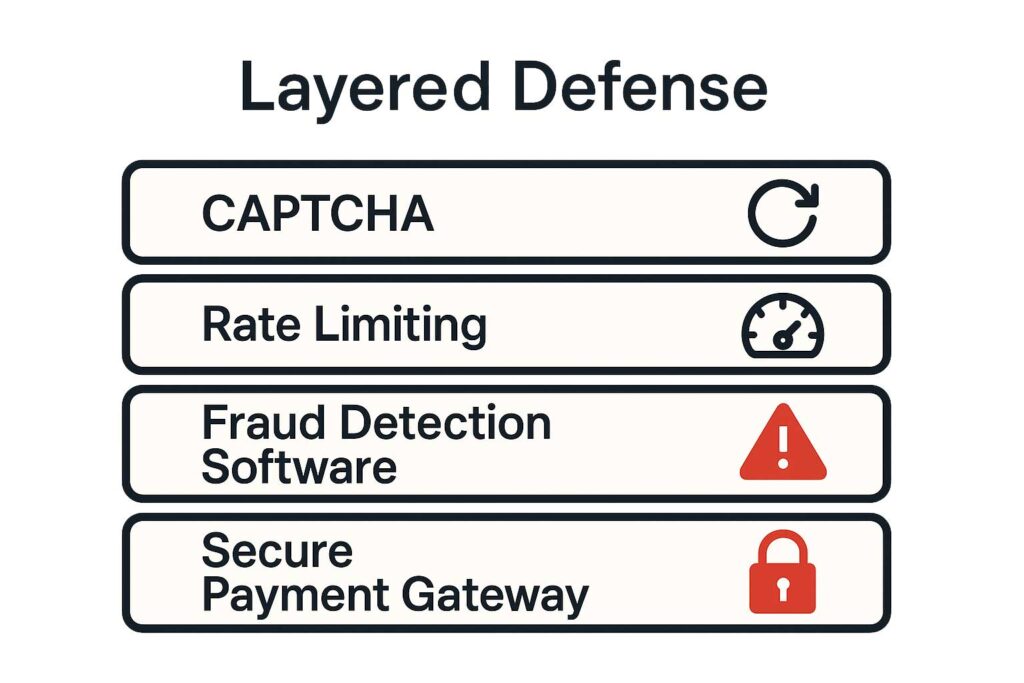
How to Protect Your Business
Fortunately, there are several practical steps you can take to protect your e-commerce site:
Technical Solutions:
- Rate Limiting: Prevent bots from making too many attempts in a short time.
- CAPTCHAs: Challenge users during checkout to ensure they’re human.
- BIN Validation: Block or flag card numbers that don’t match the expected bank issuer.
- Card Tokenization: Let your payment gateway handle the sensitive data securely.
Operational Best Practices:
- Regular Security Audits: Review your checkout and API flows for vulnerabilities.
- Employee Training: Make sure your team knows how to spot and respond to suspicious activity.
- Fraud Rules with Your PSP: Most payment providers offer fraud filters—use them wisely.
What to Do If You’re Targeted
If you suspect you’re under attack:
- Contact your payment processor immediately and report the activity.
- Block suspicious IPs or user agents that appear to be automated.
- Work with a security consultant to review your logs and identify the entry points.
- Inform affected stakeholders, including any customers who may have been impacted.
The sooner you act, the better your chances of minimizing damage.
A credit card enumeration attack might sound technical, but its impact is very real—and very avoidable. As an e-commerce business owner, your checkout process is a critical line of defense. Taking proactive steps now can save you from financial loss, customer trust issues, and potential legal headaches down the line.
Remember, a secure checkout isn’t just good practice—it’s part of your customer promise.